-
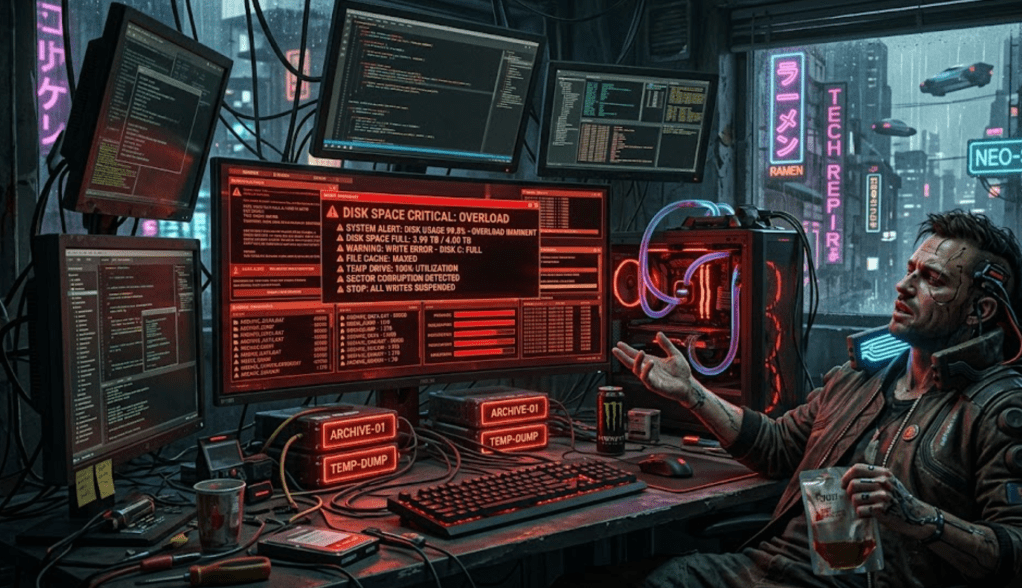
Sysmon ArchiveDirectory: When Your Security Stack Fills Your Own Disk
The scenario: A Windows endpoint slowly runs out of disk space. The culprit isn’t logs, user data, or a rogue application — it’s Sysmon, quietly archiving a copy of every…
-
Level Up Your Lab: PT3
You’ve built the attack tools. You’ve built the defences. Now it’s time to make them fight each other — and automate the whole thing. This is Part 3 of our…
-
Build Your Own Blue Team: ideas PT2
Breaking into systems is fun. Knowing when someone is breaking into yours? That’s power. If Part 1 of this series was about arming yourself with offensive tools, this post is…
-
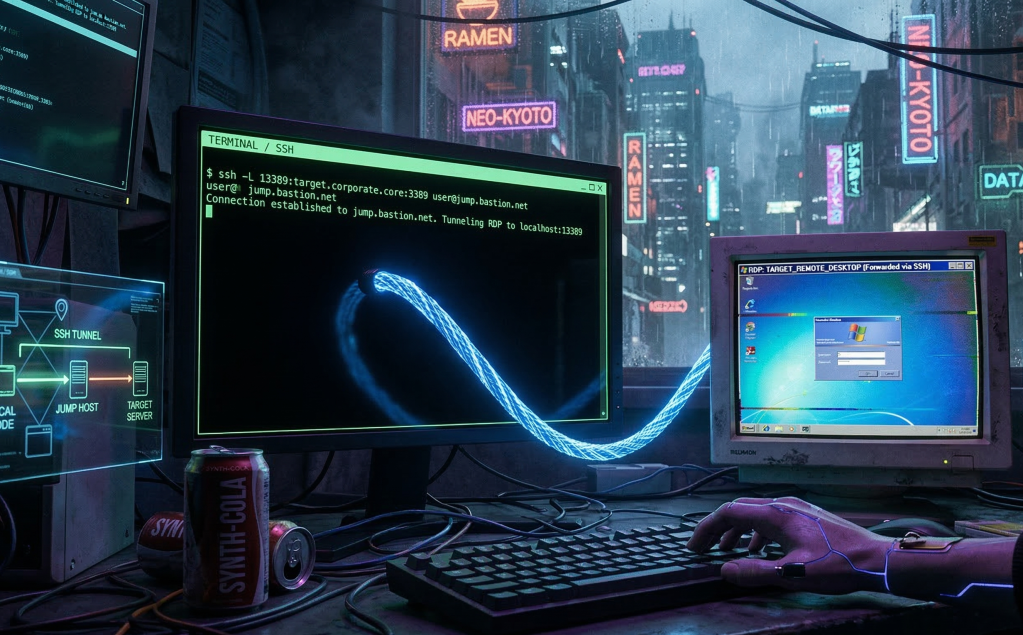
Build Your Own Attack Lab : IDeas PT1
You don’t need a six-figure budget or a corporate SOC to learn offensive security. You need a laptop, some free software, and a willingness to break things on purpose. Every…
-
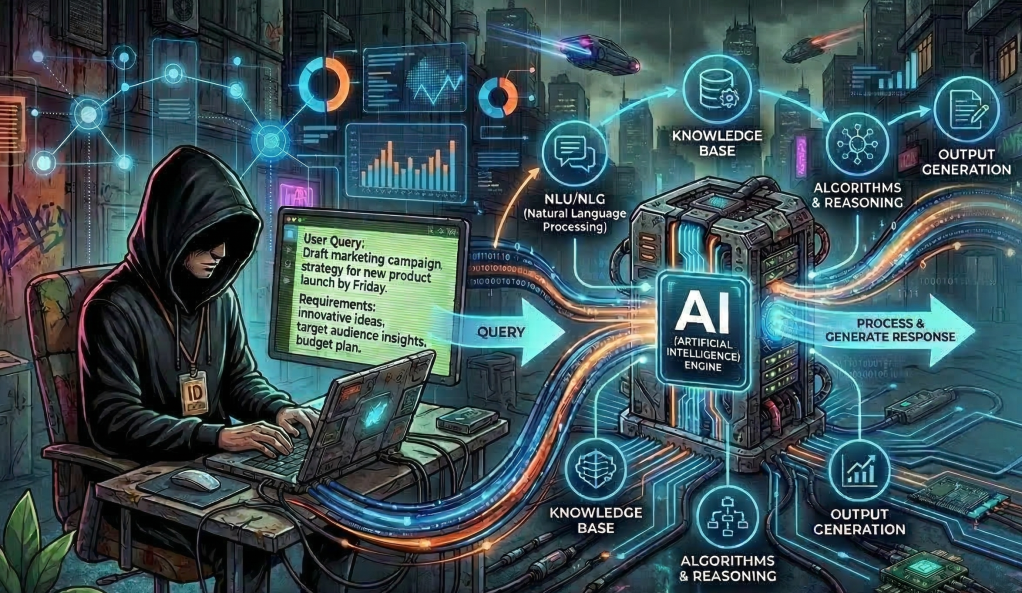
Prompts, Skills, and Agents
A reference guide for future me, so I never have to re-learn this. The One-Line Versions Everything below is expanding on those three lines. Prompts: The Starting Point A prompt…