The Spaces Between the Silos
I sat down in the lab recently to perform a simple exercise: tracing the complete path of a privileged access request. Not just the “login” moment, and not just the firewall rule, but the entire journey from the physical keyboard to the cloud console.
What I found—and what I see repeatedly in complex environments—is a dangerous fragmentation. The Endpoint team owns the laptop. The Identity team owns the MFA. The Network team owns the tunnel. Everyone owns a piece, but almost nobody owns the chain.
Adversaries don’t attack your strongest control; they operate in the “seams”—those unmonitored handoff points where one team’s responsibility ends and another’s begins. To fix this, we have to stop thinking about isolated tools and start thinking in Pipelines.
The Anatomy of the Access Journey
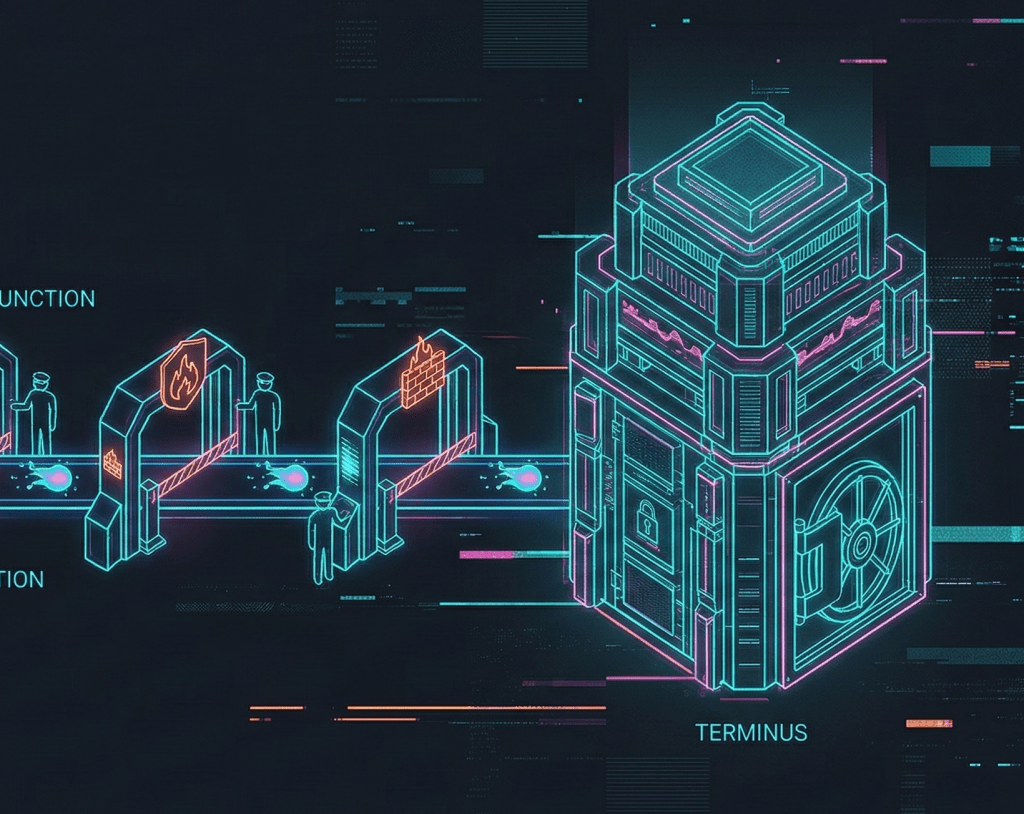
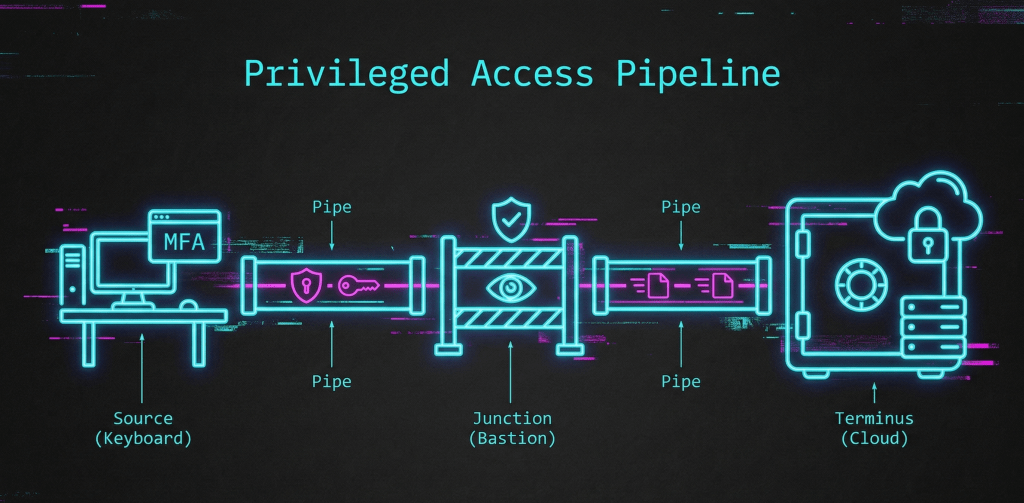
The Privileged Access Pipeline is a mental model for understanding any access request as a single governed path. It follows a relentless sequence:
Source → Pipe → Junction → Pipe → Terminus
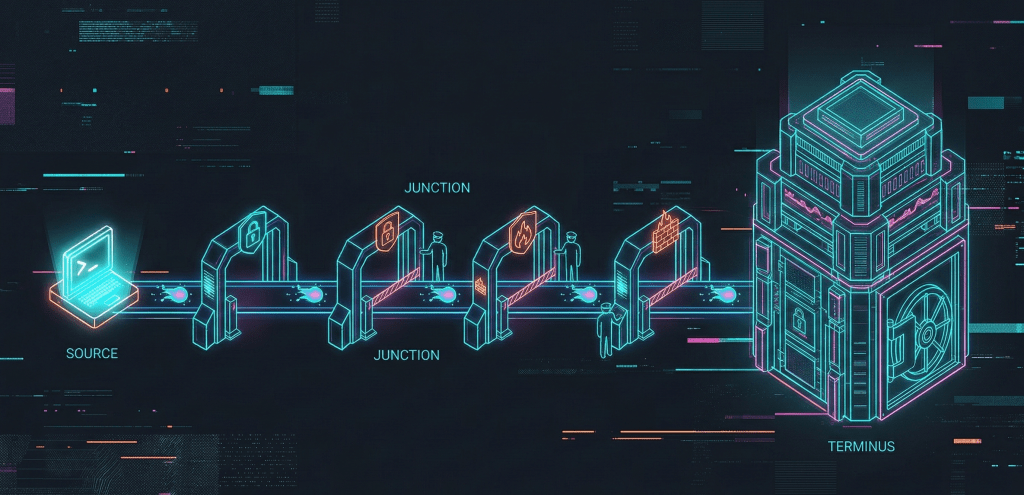
- The Source (Where Trust Begins): This is the origin point—a workstation, a CI/CD runner, or a service account. If the Source is compromised or unmanaged (e.g., a laptop with local admin rights and no EDR), the entire pipeline is built on sand.
- The Junction (The Critical Checkpoint): This is the intermediary—the bastion, the session manager, or the cloud access broker. This is where we inject credentials, record sessions, and enforce just-in-time (JIT) elevation.
- The Terminus (The Destination): The final target. This isn’t just a server; it’s the “crown jewel” destination, whether that’s a Kubernetes cluster, an OT controller, or an AI training platform.
Key Strategic Considerations
- Trust is Cumulative: A request arrives at the Terminus with a “reputation” built at every previous stage. If the Pipe is unencrypted or the Source is unverified, that reputation is tarnished regardless of how strong the Terminus password is.
- The Power of Collapse: In an incident, the pipeline is designed to be sacrificial. If a Source is flagged, the Junction should immediately “collapse,” severing the connection before the threat reaches the Terminus. This turns reactive scrambling into structured containment.
- Visibility Over Tooling: You don’t necessarily need more tools; you need to map what you have. A gap between a well-governed Junction and a blind Pipe is a risk you can only mitigate once you’ve visualised it.
I have documented several ways to test these “seams” in a Proxmox lab environment over on Blue-Lab if you want to dig deeper into the implementation.
Engineering the Chain: From Theory to Trace
When we move from the Architect’s whiteboard to the Engineer’s terminal, the pipeline becomes a series of verifiable handoffs. To understand your own pipeline, you have to audit the “Inventory” of controls at each stage.
The Pipeline Inventory Matrix
This matrix helps identify who owns which segment of the journey and, more importantly, where the “no-man’s-land” exists in your architecture.
| Stage | Primary Job | Key Controls | Typical “Blind Spot” |
| Source | Establish Baseline Trust | EDR, MFA, Device Compliance | Local Admin rights, unmanaged browser extensions |
| Pipe (1) | Secure Transport | VPN, ZTNA, TLS 1.3 | Unencrypted traffic between Source and Junction |
| Junction | Governance & Isolation | PAM, Bastion, JIT Access | Over-privileged service accounts, lack of session logging |
| Pipe (2) | Internal Transport | Micro-segmentation, NACLs | “Flat” internal networks once past the perimeter |
| Terminus | Resource Protection | RBAC, Audit Logs, MFA | Direct back-door access bypassing the Junction |
The “Seam” Test: A Lab Methodology
If you want to verify your pipeline, don’t just test the controls—test the gaps. In the lab, I use a three-step verification process:
- The Source Bypass: Can I reach the Terminus directly from the Source, skipping the Junction? If yes, your Junction is an “option,” not a “requirement.”
- The Pipe Sniff: Can I capture credentials or session data in the Pipe between the Junction and the Terminus? If the Junction injects credentials over an unencrypted Pipe, you are handing keys to anyone on the wire.
- The Identity Pivot: If I compromise a session at the Junction, does the Terminus recognise the anomaly? The Terminus should ideally require a “Cumulative Trust” signal that includes the Junction’s health.
Notes
A common misconception is that the “Junction” must be a physical server (like a legacy Jump Box). In modern cloud architecture, the Junction is often logical.
For example, a Cloud Access Security Broker (CASB) acts as a Junction by dynamically modifying IAM policies. Even if there is no “box” in the middle, the function of the Junction—interception, verification, and elevation—is still being performed. When mapping your pipeline, look for the function, not just the hardware.