Trace the complete journey of an access request—not just the initial authentication, and not just the destination permission rule. Verify the integrity of the entire path. You need a reliable answer to how any connection, from a remote user to a core internal service, navigates your infrastructure to reach a critical asset.
In a typical organisation, what you will find is not an engineered path; it is a series of disconnected, vendor-specific segments managed by siloed teams.
User endpoints, including laptops and MFA, are managed by one team. Infrastructure, covering VPNs and segmentation, is managed by another. Applications and services, the final resources, are managed by a third. This fragmentation creates a profound governance problem: you have many secure points, but you do not have a reliable chain of trust.
Every connection point between these siloed controls is an engineered weak point. A vulnerability at the handoff between User Endpoints and Infrastructure invalidates the controls at both ends. We must stop treating access as a collection of isolated products and start engineering Access Pipelines.
The Universal Blueprint: Absolute Governance
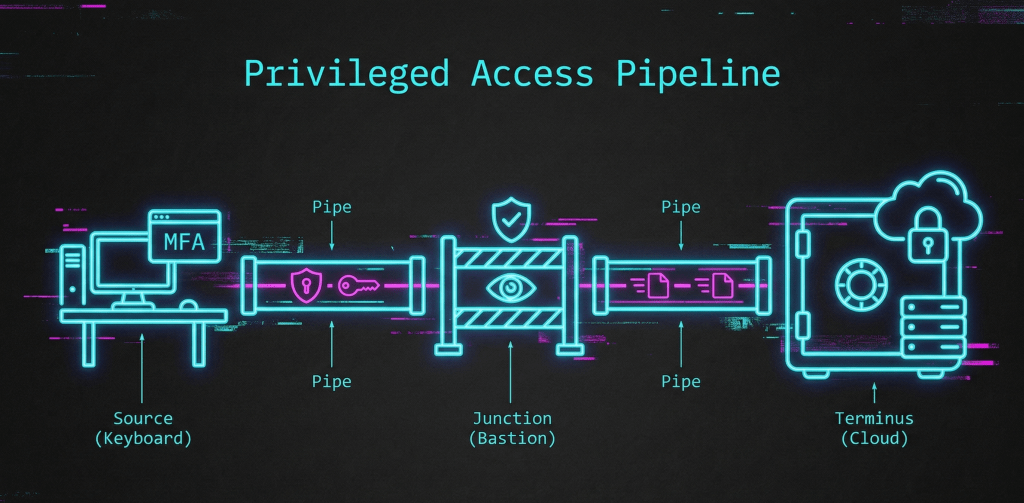
The Access Pipeline is not a product. It is a strategic blueprint—a unifying mental model that collapses complexity. It provides a single, technology-agnostic visualisation of every access request, from original origin to final destination, as a single governed path.
This agnostic framework applies to every asset, whether it is an on-premises SCADA controller, a legacy mainframe, or a dynamic Kubernetes cluster. It is not tied to a specific technology; it is the universal structural requirement for access governance.
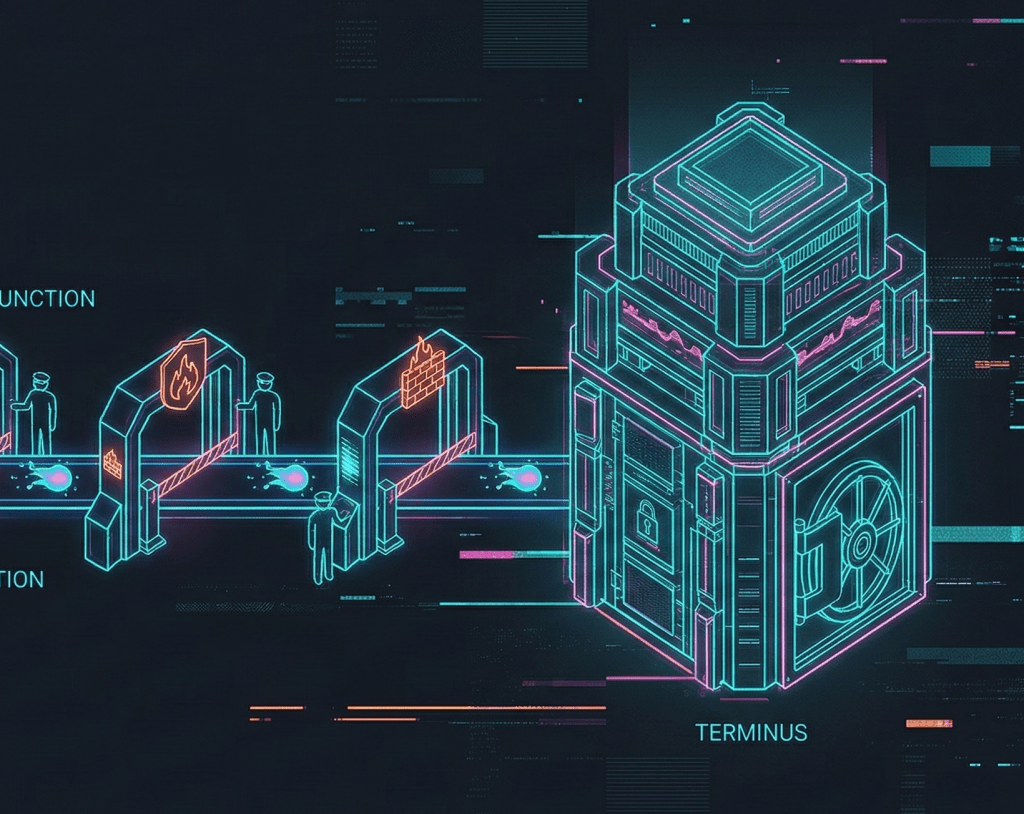
It forces you to account for the journey as three core stages, linked by two explicit interconnections:
Source → Pipe → Junction → Pipe → Terminus
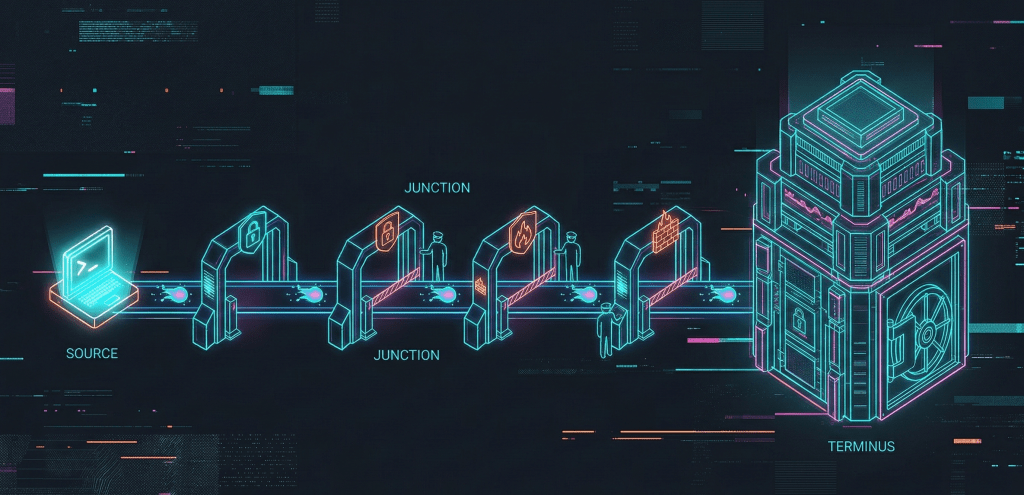
By mapping any access path to this model, we move past theory to pressure-test the architectural integrity, establishing true Defence in Depth. It helps you map exactly what controls and verifications an access journey should encounter along its path.
Engineering the Blueprint: The Control Inventory
When we move from the Architect’s whiteboard to implementation, the pipeline becomes a visual checklist of verifiable control points. To operationalise this structural model, you must audit the inventory of controls available at each stage and interconnection.
The defining metric of a structurally sound pipeline is Cumulative Trust, measured by the lossless transfer of security context between silos. A complete pipeline is validated by coordinated Defence in Depth—integrating policies, identity validation, cryptographic chains, and active monitoring across every segment.
The following matrix provides a granular breakdown of the Cybersecurity stack required to engineer integrity into the pipeline.
The Access Pipeline Inventory Matrix
| Stage | Primary Job | Key Controls | Gaps Surface When… |
| Source | Establish Baseline Trust | EDR with HIDS (Host IDS), Secure Browsers, MFA, explicit User and System Policy, Machine Identity verification, Data-at-Rest Encryption. | The Source has local admin rights, unmanaged browsers, or unverified machine identity. |
| Pipe | Secure Initial Connection | VPN / ZTNA tunnels, Encryption in Transit (e.g., TLS 1.3+), automated certificate management (PKI), Network Policy enforcement, NIDS / NIPS (Network IDS/IPS). | The Pipe has unmonitored traffic, lacks inspection capabilities, or relies on weak encryption protocols. |
| Junction | Governance & Isolation | PAM, Proxy/Broker Services, Session Recording, approval workflows, dynamic routing, explicit Policy Re-verification, Decryption for Inspection, dynamic mTLS brokering. | The Junction provides static access or acts as a passive pass-through without active policy enforcement. |
| Pipe | Safe Internal Delivery | Micro-segmentation, NACLs, Encryption in Transit, internal service-to-service Machine Identity, internal NIDS / NIPS. | The internal routing relies on a “flat” network once past the perimeter or has unmonitored connections. |
| Terminus | Resource Protection | Least Privileged Access controls (RBAC/ABAC), Resource-specific MFA, comprehensive Audit Logging, application-level HIDS / RASP, App/System Policy enforcement, Data-at-Rest Encryption. | The Terminus relies solely on perimeter controls or provides excessive privileges by default. |
Crucial Implementation Rule: A complete pipeline requires coordinated End-to-End Encryption. Encryption in Transit (across both Pipes) and Data-at-Rest (at the Source and Terminus) must be managed as a continuous cryptographic chain. Any segment lacking this integration represents a critical structural weakness.
Strategically Enable, Improve, Simplify
Pick one critical access path in your environment. Map it against this pipeline structure: Source, Junction, Terminus. This is a strategic mapping exercise, not an audit. The goal is structural clarity, using one diagram to unlock critical leadership functions:
A Unified Language: The framework provides a shared language that clearly conveys progress and architectural reality from the C-Suite down to the hands-on engineer.
Prioritising Architecture: Identify gaps, establish your baseline, and clearly define your existing architecture.
Mapping Baseline Controls: Clearly identify what has been done and what mitigating security controls exist at each stage of the journey.
Structuring Governance: Seamlessly layer processes and procedures (system and user policies) directly into the technical stack you have today.
Engineered Containment: The pipeline is collapsible by design. During an incident, you do not need to understand the entire environment before acting. If a Source is compromised, collapse that section at the Junction. Kill the session and sever the connection. This shifts your posture from reactive scrambling to executing structured containment boundaries.